Secure Information Flow for 605994876, 18006564120, 8082017835, 630124300, 6318240027, 600135180
Secure information flow for sensitive identifiers such as 605994876 and 18006564120 is critical in today’s data-driven landscape. Organizations must prioritize the implementation of advanced encryption protocols and strict access controls to mitigate unauthorized access. Additionally, data masking techniques can significantly reduce exposure risks. However, the evolving nature of cyber threats necessitates continuous evaluation of security measures. This prompts a closer examination of the best practices and technologies available to safeguard such sensitive information.
Understanding the Importance of Secure Information Flow
How does the integrity of information flow impact organizational security?
The secure transmission of data is vital in mitigating risks associated with data breaches. By implementing robust information encryption protocols, organizations can safeguard sensitive information from unauthorized access.
Ensuring the integrity of this flow not only protects assets but also fosters a culture of trust, enabling a more resilient and freedom-oriented operational environment.
Best Practices for Protecting Sensitive Identifiers
The protection of sensitive identifiers is a critical aspect of maintaining secure information flow within an organization.
Implementing identifier encryption ensures that unauthorized access to sensitive data is minimized. Additionally, employing data masking techniques can obscure identifiers in non-production environments, reducing exposure risk.
Adopting these best practices fosters a culture of security, empowering organizations to protect sensitive information effectively while promoting operational efficiency.
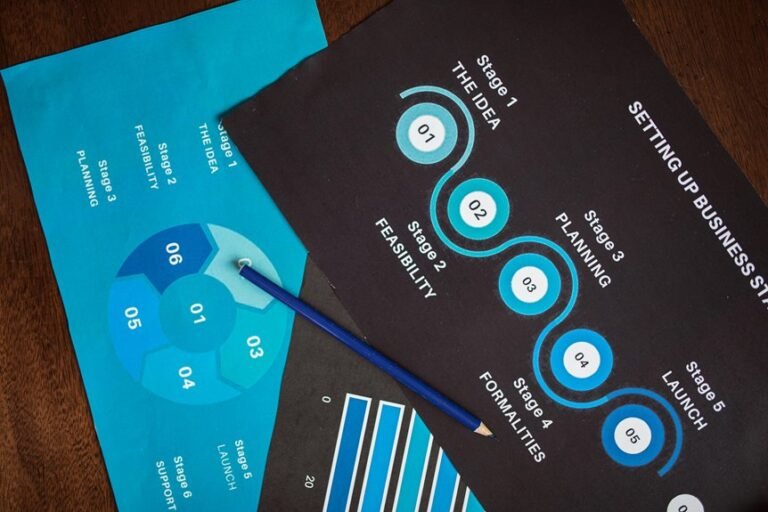
Technologies to Enhance Data Security
Numerous technologies exist to enhance data security, each offering unique capabilities to safeguard sensitive information.
Encryption methods provide robust protection by transforming data into unreadable formats, ensuring unauthorized access is thwarted.
Additionally, access controls regulate who can view or manipulate data, further fortifying security measures.
Together, these technologies form a comprehensive defense strategy, empowering organizations to maintain the confidentiality and integrity of their critical information.
Compliance and Regulatory Considerations
Organizations implementing data security technologies must also navigate a complex landscape of compliance and regulatory considerations.
Adherence to various regulatory frameworks is essential to ensure data integrity and privacy. Moreover, regular compliance audits are necessary to assess alignment with these frameworks, mitigate risks, and foster trust.
Ultimately, a robust compliance strategy empowers organizations to maintain operational freedom while safeguarding sensitive information.
Conclusion
In conclusion, the safeguarding of sensitive identifiers like 605994876 and 18006564120 is not merely an IT responsibility but a critical organizational imperative. By implementing best practices and cutting-edge technologies, organizations can create a fortress against potential data breaches. The commitment to robust security measures is akin to building an impenetrable wall in a world where cyber threats multiply like rabbits. Thus, fostering a culture of security and compliance is essential for maintaining the integrity and confidentiality of sensitive information.